Super-Malware has become intense, more common
You already know about malware and you’ve learned not to click stupid links, but your company is vulnerable in more ways than just simple viruses sent over emails, with threats coming from new and increasingly intelligent sources.
To help us better navigate these vulnerabilities for every company (even a one person operation), we tapped the wisdom of Maddie Grant, who outlines below the rise of the Super-Malware:
Threats outpace the rise of awareness
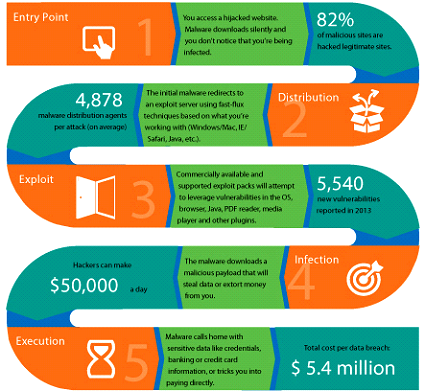
Over the last few years the volume and intensity of malicious web security attacks has grown dramatically, thanks mainly to greater access to high-powered distributed systems and automation; and exploit kits that make execution and distribution simpler for cybercriminals. The strength of attacks is daunting and though the internet community is growing more aware of general risks, the threats seem to outpace it. 2013 is dubbed the year of the mega breach, where we witnessed 253 major breaches that exposed 552 Million identities including credit card data, addresses, passwords and other personal information. This was a 62% increase over 2012 (according to Symantec).
Website vulnerability has been a very attractive starting point for cybercriminals to inject and launch their attacks. Symantec’s state of web security report reveals that 77% of the websites they researched had exploitable vulnerabilities and 1-in-8 was critical. With unchecked access to websites, cyber-criminals are left to roam free executing zero-day exploits that covertly infiltrate to not only steal data but also cripple legitimate networks.
The battle to protect your website and guarantee availability for your clients and other site visitors is a critical area of focus for your company. Depending on the reach and scope of your business and the number of clients being served, a data breach can easily cost you upwards of $5.4 Million. Thankfully, it costs significantly less to protect your web assets.
The Types of Attacks & Risk to your Business
Protecting your website and networks requires input and insight for all aspects of the services you’re providing both to clients and internally. If you’re primarily delivering a service online via a software-as-a-service model, you may be inclined to focus solely on making your web application secure at the code level; ignoring the establishment of internal network usage policies and other types of gateway level protection that will help mitigate denial of service attacks, for example.
Complete security requires an approach that not includes your developers, but IT staff, your web host and other security service providers and resources serving the application, network and human layers.
Some of the most common application layer threats are typically directed towards compromising private user data for the sake of financial gain. Through the injection of code to pull data and trick users into sharing private information cybercriminals gain access.
Examples of the most attacks include:
- Cross-Site Scripting (XSS)
- Injection Flaws
- Malicious File Execution
- Insecure Direct Object Reference
- Cross Site Request Forgery (CSRF)
- Broken Authentication and Session Management
- Insecure Cryptographic Storage
- Insecure Communications
- Failure to Restrict URL Access
While other attacks like distributed denial of service attacks (DDos) are designed to completely cripple your business’ ability to serve clients and access critical network assets. These are simply meant to hemorrhage and take your business down causing unimaginable and sometimes irreparable damage.
For these types of attacks, you certainly cannot rely on your web server host for protection. And investing in the physical infrastructure and staff to manage, implement and monitor mitigation appliances and services will definitely put a dent in your cashflow.
DDos Could be the Greatest Threat
DDos works by overloading and flooding network servers with data packets and requests to the extent where the server is unable to respond; therefore, taking down the network. DDos attacks have grown more sophisticated with packet floods growing larger, maxing out at around 100 Gbps. In a six-month campaign against U.S. banks, for which a group of alleged Muslim hacktivists claimed credit, the volume of attack traffic regularly surpassed 30 Gbps – throughput rarely seen a decade ago. The 1st quarter of 2014 saw a 240% increase in botnet activity.
Attackers also have targeted other parts of the network infrastructure. Corporate domain name service servers are a common target, and in this case, customers can no longer access a company’s service. Under these attacks, the number of data center capacity a company has is irrelevant as the requests will never reach the data center. Network availability is a critical focal point for ensure business uptime and deliverability.
These attacks have evolved far beyond the capabilities of the typical in-house network security appliance that will inevitably face an overwhelmed network. The s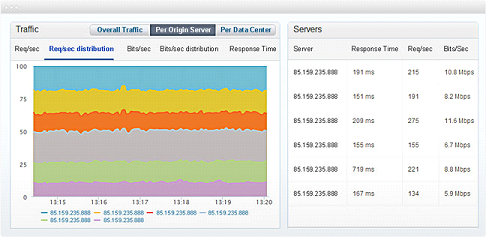 afest and most effective approach is through a hybrid approach from a security company which offers web application firewalls, CDNs, real-time monitoring and high-class network security appliances to detect and block unwanted traffic in the earliest possible instance.
afest and most effective approach is through a hybrid approach from a security company which offers web application firewalls, CDNs, real-time monitoring and high-class network security appliances to detect and block unwanted traffic in the earliest possible instance.
You’re Not Alone in the Fight & Where to Start
Security companies offering a security-as-a-service model mean that your business is saved from investing in staff and infrastructure to acquire a world-class security system. For instance, the load balancing and failover service offered by Incapsula, is very affordable, starting from $19 per month. Incapsula offers an enterprise-grade cloud-based solution supporting all in-datacenter and cross-datacenter scenarios ensuring high availability and protecting against the most powerful DDos attacks, offers instant propagation and distribution algorithms that will guarantee routing to healthy servers.
First-class infrastructure coupled with real-time monitoring capabilities mean that you and Incapsula’s team are accountable for the health of all your network assets. This is very valuable in the case of zero-day attacks that do not have known fixes, giving you the resources and data to act quickly to prevent loss.
Making the decision to migrate the management and protection of your network assets to a security-as-a-service solution, may be the best investment you could make for ensuring reliable disaster recovery and threat mitigation. It’s a sure-fire way to keep your business on the cutting edge of web security as cybercriminals become more covert and powerful.
The American Genius is news, insights, tools, and inspiration for business owners and professionals. AG condenses information on technology, business, social media, startups, economics and more, so you don’t have to.



































Pingback: Device looks like a phone charger but is tracking everything you type, yikes! - AGBeat